Page Contents
Introduction
A password, sometimes called a passcode (for example, in Linux), is confidential data, generally a series of characters customarily used to demonstrate a user’s identity. Traditionally, passwords were predicted to be remembered, but the enormous number of password-protected benefits that typical people access can make unique recollection passwords for each service unusable. A password is a dictatorial series of characters, including digits, letters, or other symbols if the allowable characters are numeric.
Despite its title, a password does not need to be an exact word; clearly, a non-word (in the lexicon intention) may be more difficult to guess, which is a seductive effect of passwords. A remembered enigma consisting of a series of words or other text divided by spaces is occasionally called a passphrase.
Both UNIX-like and Linux working systems operate the passwd command to adjust user passwords. The passwd is utilized to edit a user’s authentication receipt (password) stowed in the/etc/shade file—the passwd modification passwords for user and company accounts.
An intermediate user may only modify the password for their version. The superuser or server system (or root) may alter the password for an account. The officeholder of a company may change the password for the company. passwd also converts account details, such as the complete representation of the user, user login information, or password expiry date and intermission.
This article will demonstrate how to change a user password in Linux. Furthermore, we will guide you to force users to change their passwords the next time they log in. The teachings should work on Linux disbandments, including Ubuntu, CentOS, and Debian.
Change or set a User Password in Linux
In Linux, you can change or set the password of a user account with the passwd command.
The coded users’ passwords and different passwords associated information are accumulated in the /etc/shade file.
As an average user, you can only change or set your password. The core user and users with Sudo ownership can change another user’s passwords and demonstrate how the password can be manipulated or altered. When changing or manipulating the password, make sure you’re using a unique and robust password.
Having a solid password is a vital thing to secure your system. Often a solid password has at least 16 characters and includes at least one uppercase letter, one lowercase letter, one unique character, and one number.
For safety causes, revamping your password regularly and using a unique password for a separate account are recommended. As an average user, you own a password that protects your account, and this account includes all your vicinities and files and therefore demands necessary security.
Hence, it is a practical approach to change your password invariably to reduce the chance someone else identifies your password and can use your credentials to ascertain. When modifying a user password, make sure it satisfies the following minimal prerequisites:
- A password must be solid: at least six or eight characters or more is better.
- Make sure to use complicated passwords by combining letters, numbers, and other characters to make the password as hard to
- speculate as conceivable.
- Ensure to evade using any dictionary word as a password because assailants use a brute-force password hacker to browse the complete contents. If your password is in the lexicon, they can effortlessly break it.
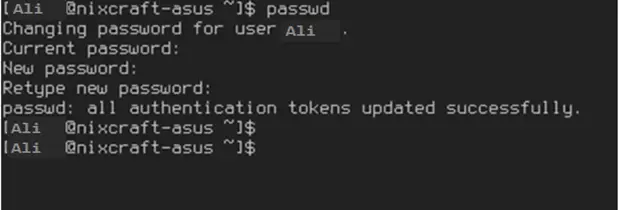
Linux Set User Password
Use the following passwd command to modify your password:
$passwd
Representative Outputs:
Changing password for Ali(current) UNIX Password:Enter new UNIX Password:Retype new UNIX Password:passwd: password revamped completely
The user is first stimulated for their old password if one is attending. This password is then encrypted and corresponds against the reserved password. The user has only one opportunity to type the correct password. The super user is allowed to bypass this step to change bypassed passwords.
Change Your User Password
To change your user’s account password, run the Passwd command without any assertions:
PasswdCopy
You will be occasion to type your subsist password. If the password is correct, the command will request you organize and verify the new password.
Passwords are not displayed on the screen when you type the new password.
The subsequent time you log in to your system, use the current password.
Linux change password for another user system
As we mentioned in the intro, just the root user and users with Sudo credentials can change the password of other users’ accounts. The following sample considers that you are logged in as a user with Sudo ownership.
To change the password of other user accounts, run the Passwd command, pursued by the username. For instance, to change the password of a user called Linuxize, run the following command:
You require to log in as the root user enter the following command to change the password for user Ali:
# Passwd Ali
OR
$ Sudo Passwd Ali
Sample output:
Enter new UNIX Password:Retype new UNIX Password: Passwd: password updated completely
Where,
Ali – is username or portrayal name. Passwords do not show on the screen when you enter the password. For example:
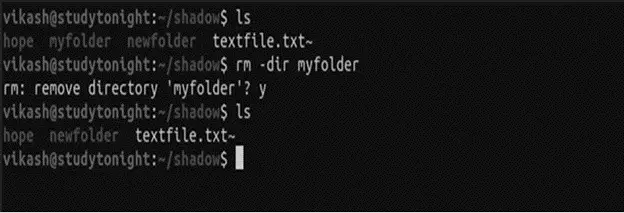
Deleting a Password
This alternative sets an account practically password-less so that everyone can log into it. This is not good in most individual systems, but for a home Personal Computers, that’s what most individuals use, or for a system that requires to be open to everyone who tries to use it, this choice is essential. This command also demands a root permit. To delete the password of a user, utilize the following syntax:
Sudo Passwd -d <username(Ali)>
Model output:
Pulkit@hostname:~$ Sudo passwd -d (user)[Sudo] password for pulpit: Passwd: password expiry details changed.Pulkit@hostname:~$
Force User to Change Password at Login
By choice, passwords are developed that never expire. To force a user to alter their password the following time they log in, utilize the Passwd command with –expire option pursued by the username of the user:
$ Sudo passwd –expire linuxize.Copy
The command overhead will instantly expire the user password.
The next period the user attempts to log in with the old password, they will be displayed a notification forcing them to change the password:
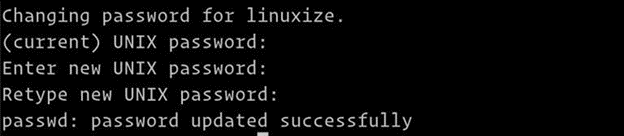
$ ssh linuxize@192.168.121.101Sample OutputWARNING: Your password has expired.You must adjust your password directly and log in again!Changing password for linuxize.UNIX password(current):Enter new UNIX Password:Retype new UNIX Password:Passwd: password updated successfullyConnection to 192.168.121.101 closed.
Once the user establishes a new password, the association will be locked.
The Passwd command in Linux is used to change user passwords effectively. This command edits an authentication password/token for a user held in your system’s /etc/shade file. A typical user in Linux can change their password. Nonetheless, a superuser can also modify the password for other users. Choosing a complex one is a good security practice when selecting a new password. A complicated and protected password has the subsequent effects:
- It possesses both upper and lower case letters
- It is different than your prior passwords
It does not retain your full name, address, mobile number, license number, or birth date. These details can easily be used to speculate your password.
Constantly note down your password in a protected location from where it can not be conveyed. It would assist you in recognizing the password in case you ignored it.
A message about setting up a specific Linux password
Centers in password protection typically result from reckless password selection. Avoid specific passwords such as:
- Words that arise in a dictionary
- Your name
- Pet names
- Kids or partners names
- License number
- Date of birth (DoB)
- Home address
I recommend developing a unique password for all user accounts using your chosen password administrator.
Verdict
That is all for the effective operations about changing user passwords in Linux. Some of these possibilities are exclusively for the root user, but that creates purpose even for individual systems, as user administration is often demanded in case of password loss or something else of the kind. The root user is permitted to overthrow any other user. The root account is not something to be recreated around with. You must consistently use the root account carefully.
Another typical use case is in servers. The upside to operating a server is that you can always access the server through a web console or internet in some circumstances, consistent if you shut yourself out of the server.
These instructions operate for any Linux distro, including Ubuntu, Debian, Fedora, CentOS, etc.